The Endpoint Has Moved to the Browser. Your Security Tools Haven't.
Your critical data no longer lives behind a firewall. It flows through browsers accessing Salesforce, Microsoft 365, and dozens of SaaS apps creating a massive visibility gap where your most valuable data is most exposed.
Download our free eBook to understand how this shift happened and what you need to do about it.
Visibility Gap Insights
90% of enterprise applications are now accessed through browsers, yet most security tools have zero visibility into browser activity.
Acium places controls where modern work happens, inside the browser so you can see, understand, and stop risk in real time.
Encrypted Traffic
Network tools miss TLS-inspected browser sessions.
Shadow SaaS
Unsanctioned apps bypass traditional controls.
AI Usage
Prompts can expose sensitive data instantly.
Extension Risk
Excessive permissions create lateral movement paths.
Three Critical Threats Converging Inside Your New Perimeter
Risky Extensions
Productivity tools your employees love operate with excessive privileges, creating an unmanaged attack surface that traditional security can't see.
AI Data Leaks
Every prompt submitted to ChatGPT or other AI tools is a potential data breach, leaking trade secrets and sensitive information beyond your control.
Fragmented Browser Security
Managing security across Chrome, Edge, and Safari creates inconsistent controls and blind spots that attackers exploit.
Your Traditional Security Stack Can't Protect What It Can't See
Legacy tools were built for a different era. Today's browser-first workflows expose critical blind spots in your security posture.
Network Security
Can't decrypt and inspect encrypted browser traffic in real time, leaving TLS sessions completely opaque.
Endpoint Agents
Lack the context to understand what's happening inside browser tabs and can't control web-based actions.
CASB Solutions
Only see sanctioned apps, missing shadow SaaS, AI tools, and the thousands of unmanaged web services.
DLP Tools
Can't control data once it enters the browser environment or prevent copy/paste into AI models.
The Browser Visibility Gap
90% of enterprise applications are now accessed through browsers, yet most security tools have zero visibility into browser activity. Security controls stop at the browser door, leaving data flows uninspected and policies unenforced.
Turn Your Biggest Blind Spot Into Your Strongest Defense
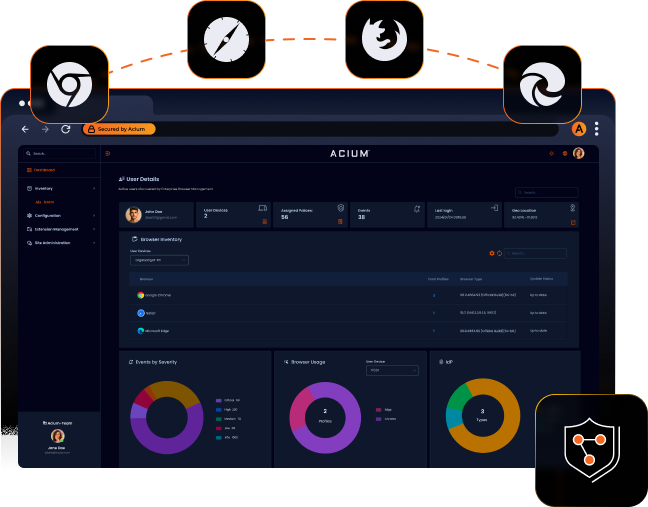
Acium Unified Browser Security gives you real-time visibility and granular control over all browser activity across every browser, every device, every user.
Complete Browser Visibility
Monitor every action, copy/paste, screenshots, downloads, uploads, and AI prompts across Chrome, Edge, and Safari from one dashboard.
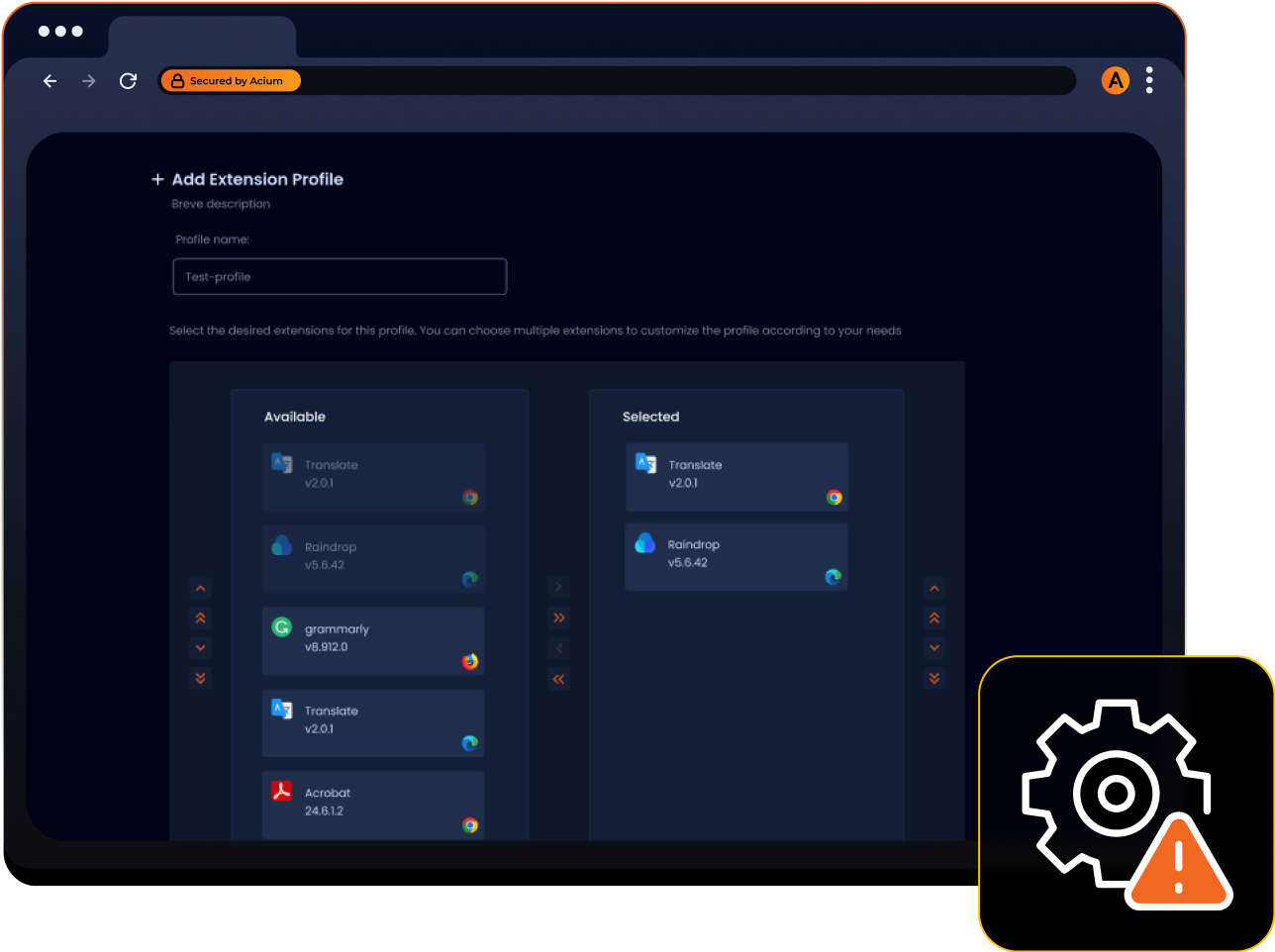
Intelligent Extension Control
Automatically scan and risk-score all browser extensions. Block malicious activity instantly while maintaining granular control over approved tools.
AI-Aware Data Protection
Prevent sensitive data from being typed or pasted into ChatGPT, Claude, and other AI tools with context-aware DLP policies.
Unified Cross-Browser Management
Apply consistent security policies across all browsers and devices, corporate, BYOD, and contractor equipment from a single console.
Real-Time Threat Detection
Leverage a database of 1B+ URIs to identify and block phishing, malware, and malicious sites within minutes, before they reach your network.
Zero Trust Browser Security
Implement granular access controls and data policies based on user, device posture, location, and application with no VDI required.
Secure the New Endpoint in Minutes, Not Months
Deploy
01Simple browser extension deployment via Google Admin, Microsoft Entra ID, or manual install. No infrastructure changes required.
Configure
02Set policies for extensions, AI tools, data controls, and web filtering from an intuitive dashboard. Apply rules by user, group, or device.
Protect
03Real-time enforcement and monitoring begins immediately. Users keep their preferred browsers and workflows security works invisibly.
Integration Callout
Integration-ready with your existing SIEM, directory services, and security stack.
One Platform, Complete Browser Protection
Eliminate Shadow SaaS
Automatically discover every web application your team uses. Monitor for risky behavior and implement policies to prevent data leakage without blocking productivity.
Browser Security Built for the Modern Enterprise
Browser Agnostic
Chrome, Edge, Safari, manage them all.
Device Agnostic
Corporate, BYOD, contractor devices.
Deployment Flexibility
Minutes to deploy, no infrastructure changes.
User Experience
Works invisibly, maintains productivity.
Standards-Based
OCSF-compliant data for easy SIEM integration.
Comprehensive Control
600+ browser settings, granular policies.
Data Sovereignty
Control where data is stored and processed.
Integration-Ready
Works alongside your existing security stack.
📖 FREE EBOOK - Expert Insights & Data
The Browser as the New Endpoint
A comprehensive analysis of why your security stack has a critical visibility gap and how to fix it.
Key Topics Covered:
- The Great Migration: How the browser became the enterprise endpoint and what this means for your security architecture
- Three Critical Threats: Browser extensions, AI data leaks, and multi-browser chaos converging inside your new perimeter
- The Visibility Gap: Why traditional security tools (firewalls, endpoint agents, CASB, DLP) are architecturally blind to browser activity
- Strategic Framework: How to achieve unified visibility and control directly within the browser
Key Statistics & Insights:
$315B → $1.1T SaaS market growth by 2032
$10.22M average data breach cost
44% of security incidents originate in the browser
78% of organizations increasing cybersecurity budgets