April 14, 2026
Your firewalls are configured. Your EDR is deployed. Your email gateway catches phishing attempts before they reach inboxes. Your security stack looks solid on paper.
Then you turn on browser visibility for 7 days, and everything changes.
At Acium, we run Browser Security Health Checks for organizations across industries. The process is simple: deploy our lightweight browser extension in silent mode, let it passively observe browser activity for 7 days, and deliver a Risk Exposure Report with concrete findings. No disruption. No blocking. No alerts. Just visibility.
We have now analyzed the aggregated, anonymized results from these assessments. The patterns are consistent, the findings are alarming, and the conclusion is unavoidable: the browser is the largest unmonitored attack surface in enterprise security today.
Here is what organizations typically discover in their first 7 days.
1. The Extension Problem Is Worse Than Anyone Expects
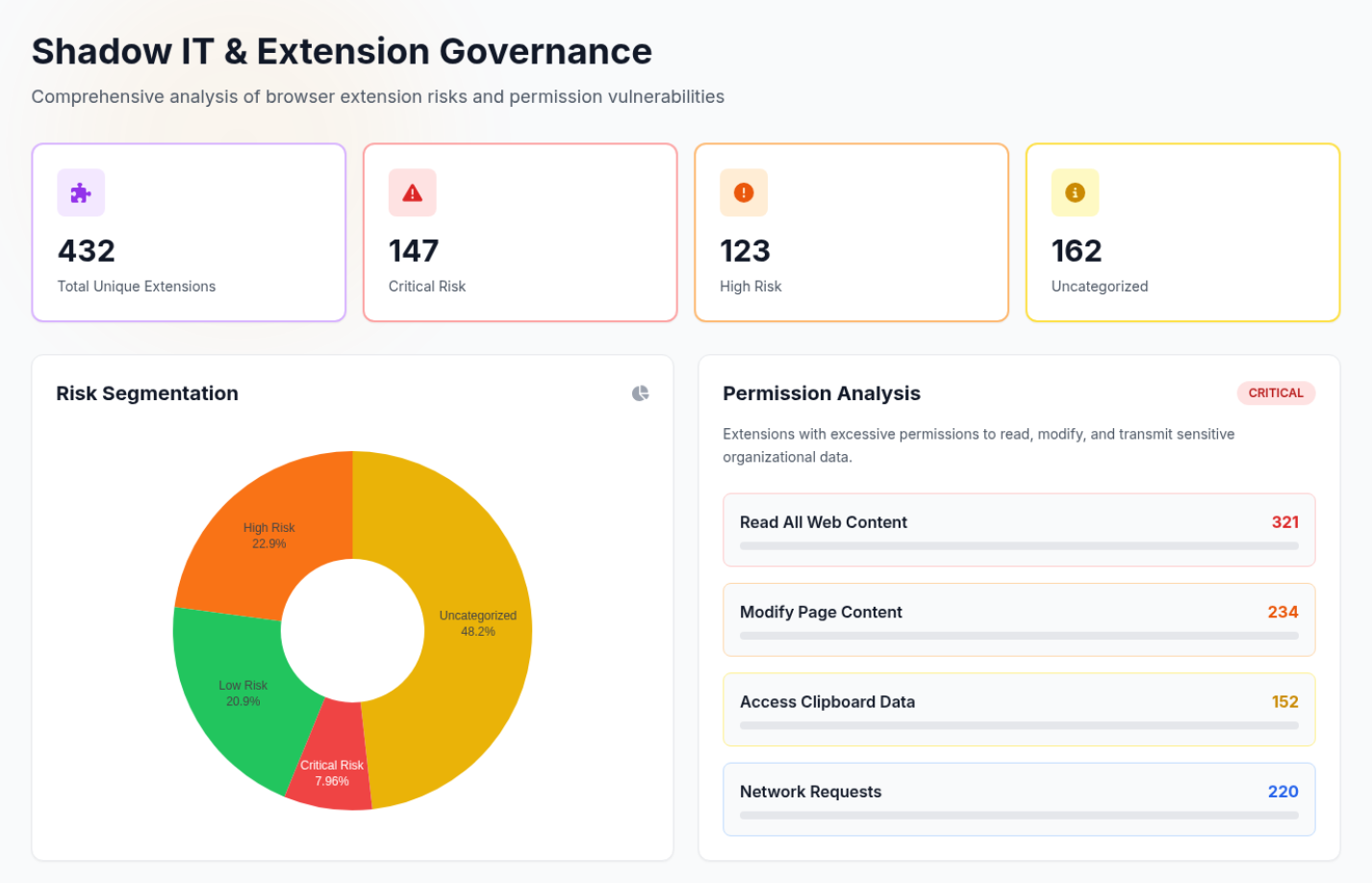
Every Health Check begins with a full inventory of browser extensions across the organization. This is where the first shock happens.
The average mid-size organization (1,000 to 5,000 employees) discovers 614 unique browser extensions in their environment. Of those, only 24% are managed through IT policy. The remaining 76% are a mix of unmanaged extensions installed by employees, personal extensions synced from consumer Chrome profiles, and extensions that no one on the security team has ever reviewed.
Here is how the risk breakdown typically looks:
| Risk Level | Avg % of Extensions | What It Means |
|---|---|---|
| Safe | 18% | Known, reviewed, low-permission extensions |
| Low Risk | 27% | Minimal permissions, generally benign |
| Medium Risk | 22% | Moderate permissions that warrant review |
| High Risk | 19% | Broad permissions including access to browsing data |
| Critical Risk | 14% | Full read/write access to all web data, or known malicious behavior |
That last row is the one that keeps CISOs up at night. In a typical 614-extension environment, roughly 86 extensions have critical-risk permissions. These extensions can read and modify every page the user visits, intercept form data, access cookies, and exfiltrate information silently. In one assessment, we discovered 11 extensions with permissions to read all clipboard data, meaning every password, API key, and sensitive snippet that an employee copied was accessible to a third-party extension developer.
The real issue is not just the number. It is the invisibility. Before the Health Check, the security teams in these organizations had visibility into zero of these critical-risk extensions. They were not monitored by EDR. They were not governed by CASB. They were not included in any vulnerability management program. They simply existed, undetected, with full access to sensitive data.
One financial services firm with 2,400 employees discovered 847 unique extensions. Among them: 23 extensions with critical-risk permissions, including one that had been silently exfiltrating browsing history to an overseas server. Their security team, which had invested millions in perimeter and endpoint protection, had no idea.
2. Employees Are Pouring Data Into AI Tools
The second section of every Health Check report quantifies something most security teams suspect but cannot prove: the scale of data flowing into generative AI tools.
The average organization sees 3,180 clipboard paste events into LLM platforms during a 7-day Health Check. That is roughly 454 paste events per day, meaning employees are copying and pasting content into ChatGPT, Google Gemini, Claude, Perplexity, and dozens of other AI platforms hundreds of times every single day.
But the clipboard events are only part of the story. In a typical Health Check, we also detect:
- 47 unique GenAI and LLM platforms accessed by employees (most organizations are aware of 3 to 5)
- 189 file uploads to AI platforms during the 7-day window, including spreadsheets, PDFs, code files, and documents
- 312 file downloads from LLM sessions, often including AI-generated code or content that may contain hallucinated or insecure outputs
- 478 "Login with Google" or "Login with Microsoft" events on unvetted AI platforms, meaning employees are creating corporate-linked accounts on tools the company has never approved
That last data point is particularly concerning. Every SSO login event represents a new corporate identity created on a third-party platform without IT approval. These accounts persist, they accumulate data, and they create compliance exposure that most organizations cannot even begin to quantify because they do not know the accounts exist.
One healthcare organization with 3,200 employees was particularly surprised. In 7 days, they detected 4,247 clipboard paste events into AI tools, 67 file uploads (including files with naming conventions that suggested patient-related content), and 513 corporate SSO logins to 47 different AI platforms. Their existing DLP solution, which monitored email and cloud storage, had flagged zero of these events.
3. Shadow IT Lives in the Browser Now
The traditional definition of Shadow IT focused on unauthorized servers, unsanctioned cloud accounts, and rogue SaaS subscriptions. The Health Check reveals a new reality: the most pervasive Shadow IT in the modern enterprise lives inside the browser.
The average Health Check identifies 127 SaaS applications actively used by employees that are not on the organization's approved software list. These range from project management tools and design platforms to file converters, code editors, and niche industry applications.
The web traffic analysis section of the report maps:
- Top visited SaaS applications by category, revealing which tools employees actually rely on versus which ones IT has provisioned
- Most frequented external websites, often surfacing domains that fall outside corporate policy
- Active web category distribution, showing where employee browser time is actually spent
- Geographic access patterns, identifying anomalies like logins from unexpected locations
In one manufacturing company with operations across 4 countries, the Health Check revealed that 34% of all SaaS application usage involved tools that were completely outside IT visibility. Employees had adopted their own project management platforms, file sharing services, and communication tools because the approved options did not meet their needs. None of this usage was malicious, but it represented a massive governance gap. Data was moving between sanctioned and unsanctioned applications through the browser, and no security tool in their stack could see it.
The pattern is the same everywhere we look. Browser-based SaaS adoption moves faster than IT governance. Employees find the tools they need, authenticate with corporate SSO, and start working. By the time the security team learns about it — if they ever do — months of sensitive data have already flowed through platforms with no contractual, compliance, or security review.
4. Threats and Compliance Gaps Hide in Plain Sight
The Threat and Compliance section of the Health Check surfaces findings that are particularly relevant for organizations navigating regulatory requirements.
The average Health Check detects 218 PII exposure events during the 7-day window. These are instances where personally identifiable information — Social Security numbers, credit card numbers, email addresses, phone numbers — is detected in transit through the browser. Some of these events are legitimate business activity. Many are not.
The file payload analysis adds another dimension:
- Average of 1,847 file downloads detected during the 7-day period
- 6.2% of downloads are executable files (.exe, .msi, .dmg), which may represent potential malware vectors
- 11.4% are compressed archives (.zip, .rar, .7z), which can obscure malicious payloads
- 29.3% are documents (.pdf, .docx, .xlsx) downloaded from external sources that bypass traditional DLP
The safe browsing verification data is actually one of the brighter spots. Acium's real-time URL scanning typically verifies a 99.7% safe browsing rate, meaning the overwhelming majority of URLs employees visit are safe. But that remaining 0.3% can represent hundreds of potentially dangerous page visits in a 7-day period for a mid-size organization, and these are visits that occur entirely within the browser, invisible to network-level security tools.
One professional services firm discovered during their Health Check that employees had downloaded 43 executable files from domains that were not on any approved list. Their endpoint protection would eventually scan these files, but the download activity itself — the intent and the source — was invisible to every other tool in their stack until Acium surfaced it.
5. The Gap Between Perception and Reality
Perhaps the most valuable finding from aggregating Health Check data is not any single metric. It is the gap between what organizations believe their security posture looks like and what 7 days of browser visibility actually reveals.
Before a Health Check, most organizations believe:
- They have visibility into the software running on employee devices (they do not have visibility into browser extensions)
- Their DLP covers sensitive data movement (it does not cover browser-based data flows to AI tools)
- They control which SaaS applications employees use (they control which ones they provision, not which ones employees adopt)
- Their compliance posture is strong (it has a browser-shaped hole in it)
After a Health Check, the conversation shifts. The data is their own. The findings are specific to their environment. The risks are not hypothetical.
We consistently see the same reaction from security leaders reviewing their Health Check results for the first time. It is not disbelief. It is recognition. They suspected the browser was a blind spot. Now they have the data to prove it, and more importantly, the data to justify action.
From Findings to Protection
Every Health Check report ends with a section that matters more than any data point: recommended policy actions. Based on the specific findings from each organization's 7-day assessment, the report identifies immediate wins — policies that can be activated right away to close the highest-priority gaps.
These typically include:
- Block critical-risk extensions identified during the assessment
- Alert on clipboard paste events into AI tools to give security teams visibility before enforcing policy
- Restrict file uploads to unsanctioned platforms to prevent data leakage
- Enforce extension governance policies requiring IT approval for new extensions
- Activate web filtering rules based on the shadow SaaS applications discovered
The transition from silent mode to active protection is designed to be immediate. The Health Check proves the problem exists. The policy recommendations provide the path forward. And because the data comes from the organization's own environment, the urgency is built into the findings.
See What Your Security Stack Is Missing
The browser is where your employees spend 90% of their working day. It is where they access SaaS applications, interact with AI tools, install extensions, handle sensitive data, and make authentication decisions. And for most organizations, it is the one place their security stack cannot see.
A 7-day Health Check changes that. No infrastructure changes. No user disruption. No obligation. Just 7 days of visibility that reveals what your firewalls, EDR, and CASB have been missing.
Deploy in minutes. Results in 7 days. See what you have been missing.
The data points in this article are derived from aggregated, anonymized Health Check assessments and represent typical findings across mid-market and enterprise organizations. Individual results vary based on organization size, industry, and browser usage patterns.
About Acium
Founded in November 2024, Acium is the pioneer in Unified Browser Security™. The company's patent-pending technology protects and manages every browser in an organization from a single, intuitive hub, offering unparalleled visibility, control, and real-time threat protection. With advanced extension risk scoring, Acium helps businesses identify and mitigate threats from risky browser extensions, strengthening security without disrupting workflows. Acium enables organizations to keep their preferred browsers while safeguarding sensitive data, ensuring secure browsing, and simplifying management.
Media Contact:
The Author